 When Google began encrypting its search referral traffic back in October 2011, I speculated it would change the analytic world as we know it even though Google estimated it would only affect single-digit percentages of search referral traffic.
When Google began encrypting its search referral traffic back in October 2011, I speculated it would change the analytic world as we know it even though Google estimated it would only affect single-digit percentages of search referral traffic.
Until today, both my pessimistic prophecy and Google’s estimation didn’t turned out to be accurate as the percentages of encrypted search referral data were stabilized at somewhere in the middle. But now, I have to raise my early prediction (and fears) one more time…
The company’s software engineer Michael Safyan has announced on Google’s Inside Search Blog yesterday that over the next few weeks the company will begin rolling out its encrypted search of logged-in users for all other Google domains across the world.
It means that in addition to Google.com which mostly serving English-speaking users from the U.S., all other local domains such as Google.fr (in France), Google.co.in (in India) and Google.co.uk (in the U.K.) would also gain SSL encryption. You can identify it if you see https:// instead of http:// at the beginning of the URL (note the additional “s”).
With the arrival of encrypted search into the global arena, it would probably increase drastically the number of unidentified (“not provided”) keywords in the webmaster’s analytic tools, make it even harder to understand and optimize incoming Google search traffic. For example, take my own Google keywords distribution from the beginning of the year:
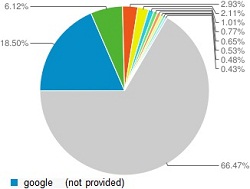
As you can see, 18.5% of Google’s search incoming traffic is marked as “not provided” (meaning encrypted). If considering that about 40% of my total Google traffic comes from the U.S., with the global expansion of encrypted search it would probably add up additional 11% of incoming “not provided” traffic (0.6*0.185=0.111).
Sites that relies more on non-U.S. traffic will probably see a much greater relative increase in “not provided” organic search traffic.
But what if the expansion of encrypted search is just a preparation for something else? Few months after the initial roll out of the U.S. encrypted search, Google has launched Search Plus Your World (which requires SSL encryption). Does Google intends to launch its controversial social search worldwide?
I am guessing that the chances we will see Google+ personalized results all over Google’s local domains soon, are pretty high. Google obviously wishes to expose its social network to more international audience where today most of Google+ users comes from the U.S. and what better way (although dubious) to do it than a deep integration into its highly popular country-based local domains?
But Search Plus Your World speculations aside, truth be told, even though webmasters are concerned and complains, encrypted search is something that actually benefit for the users privacy. And after all the company’s new privacy policy negative fallout, Google definitely needs a win in this area.